The Deep Web
Uses + Privacy + Access + Hackers + Terms
By Stepha Poulin | Spring 2017
With the recent passage of the bill that blocks regulations preventing Internet service providers (ISPs) from selling their customers’ web history, some people may be searching for a way to regain their privacy.
Without the regulations, it is perfectly legal for ISPs to search through your web history and find information like age, location, name and other personal data. Customers can avoid this in very few ways, like changing providers.
ISPs can also look at the trends in their customers’ web use and sell the information to advertisers. It’s like how an iPhone will alert the user when an Apple Store is nearby, simply using one’s location.
However, ISPs will be making a much larger profit through selling this information. Hopefully, future legislation will be passed that allows customers to opt-out of any programs that involve the sale of their Internet usage patterns.
For now, all we can do is wait. Before the passage of this bill, your Internet privacy was hardly private. That’s why some people make use of what most call the “deep web.” Its name makes it sound like the bottom most layer of the Internet. Some may assume that it is only made up of a few hundred websites. In actuality, the
Before the passage of this bill, your Internet privacy was hardly private. That’s why some people make use of what most call the “deep web.
deep web makes up the majority of the Internet — only 4 percent of the Internet is viewable with a typical Internet browser. What separates the deep web and the open web is how they are accessed.
The deep web consists of unlisted websites that make use of special web addresses. These websites cannot be accessed through mainstream search engines, which makes them difficult to find.
A typical web browser like Chrome or Firefox can only let the user access a small percentage of the entire Internet. Those who use the deep web gain access to an unfathomable amount of databases, and many are on extremely specific subjects. But how can the deep web help with privacy?
TOR is the program one would use to access the deep web. It stands for “the onion router.”
Similar to how Shrek can be compared to an onion, so can the TOR browser: it has many layers. The layers of the metaphorical onion that is TOR are actually a way to encrypt the signals sent and received to access websites.
Encryption works by taking that information and hiding it under layers of other data. This method makes it difficult to track where the encrypted data was sent or received.
A normal web browser will gain access to a website through the easiest route possible. If you are accessing the BGSU website, you will gain access to the page after the information is sent to the ISP
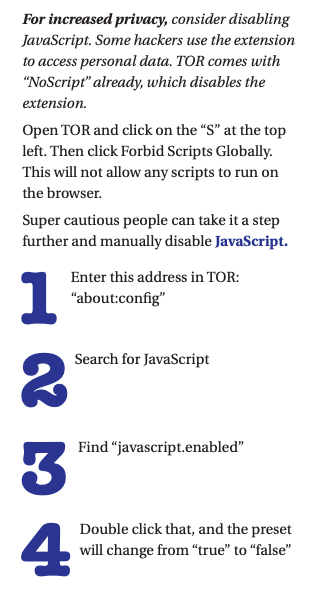
Using encryption services like TOR makes information harder to track, but there are skillful people that know TOR’s weaknesses.
Only 4 percent of the Internet is viewable with a typical Internet browser.
and then to the website’s servers. The path the information takes to get from the ISP to web servers is easy to understand for computer s cience professionals.
Therefore, it is easily trackable. Think of it this way: just as taxonomy classifies animals in a certain ranking system, the “normal” Internet carries out commands in a set order. It can be compared to genus, species, family and the other levels of the taxonomic rank.
Using encryption services like TOR makes information harder to track, but there are skillful people that know TOR’s weaknesses. Malicious TOR websites might track web usage using “exit nodes.”
Exit nodes are websites that let a user exit the deep web and enter the open web. When a TOR user accesses an exit node, the webpage will log the relays used to access the page.
If someone with malicious intent is the owner of the exit node, they gain the ability to access sites that are intended to be anonymous.
However, this is a small problem when you consider the size of the deep web. With over 1,000 exit nodes, only about 65 have been found to be malicious websites. Investigators can use exit nodes to keep track of illegal activity on the deep web.
Sites like the Silk Road have been shut down due to illicit things like drug trafficking. Of course, there are other means of tracking someone’s deep web history. Hidden service directories (HSDirs) are how sites on the deep web are relayed.
There are over 3,000 HSDirs that a TOR user can use to access specific deep websites. When used as intended, none ofthe addresses are stored by the HSDirs. But some HSDirs do store that information.
Someone can modify their HSDir to store the links and the specific services accessed through it. Links to a deep website are usually hidden. Usually, a TOR user must manually sift through the deep web to find a specific website. When the site is found, whoever made the HSDir (possibly law enforcement or hackers) can store the information used to access the site and then continually access websites that are intended to be secret.
Other members of the deep web community want to take more drastic measures — like creating a completely new onion service, or services.
Of course, there is some monitoring of the ways to store private information on the deep web.
The TOR Network tries to control this problem by identifying malicious HSDirs, and kicking them off the deep web. Other members of the deep web community want to take more drastic measures — like creating a completely new onion service, or services.
TOR developers have been experimenting with new ways to make the deep web more anonymous. Tests have been done on small networks of laptops that simulate the deep web successfully.
However, a small network isn’t enough to prove it will work. Average Internet users may find the deep web daunting. The websites found throughout it look nothing like a typical webpage.
Most look like they came straight out of the ‘90s, since most TOR website designers aren’t dedicated to looks (or easy ways to access information). They might design a website that makes someone solve a series of codes and puzzles before accessing a database. Even once the database is reached, the links could be broken because they’re more than a decade old. Yet, even
Those who prefer the open web might benefit from the use of a virtual private network (VPN) to maintain privacy on the Internet.
Facebook offers a TOR version of their open website. Those who prefer the open web might benefit from the use of a virtual private network (VPN) to maintain privacy on the Internet. VPNs can operate on the open web.
You must be sure you trust the VPN being used. A VPN could easily track and sell data.
Rather than the request to access a webpage going to the ISP, it is sent to the private servers of the VPN. Your ISP won’t have a list of the specific websites visited. Instead, it will appear that you have accessed a single server.
Then again, you must be sure you trust the VPN being used. A VPN could easily track and sell data. Some websites even discourage the use of VPNs.
Netflix tries to block all VPNs so people can’t access content that is not available in their home country. Multiple websites block specific VPNs, as certain criminal organizations or hackers may use them to hide their misdeeds.
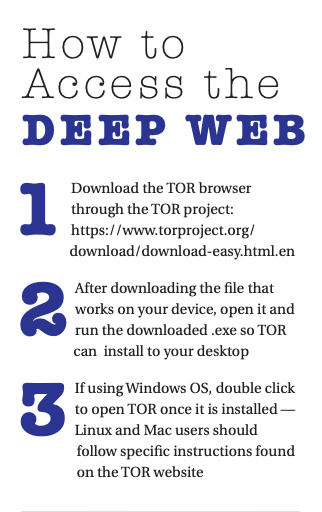
If this information hasn’t deterred you, here’s a simple guide on how to access the deep web. By the way, using TOR is completely legal. But all laws still apply, even when someone thinks they are safe due to increased (yet not complete) privacy.
Those who prefer the open web might benefit from the use of a virtual private network (VPN) to maintain privacy on the Internet.